2025 Sustainability Report
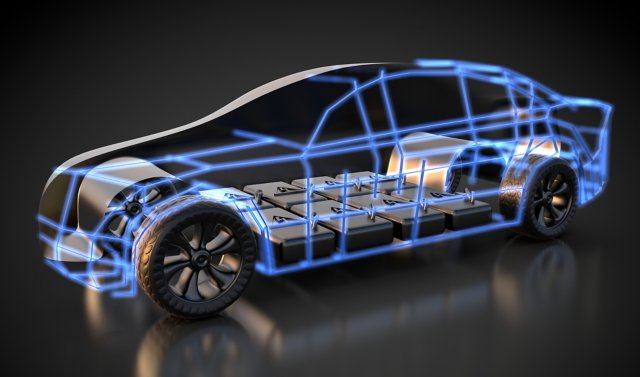
Bringing together technology and manufacturing for a more sustainable tomorrow - for our customers and for ourselves.

Future Trends in Industrial Operations
Accelerate your shift from automation to autonomy with a clear strategy and real-world examples that empower people, drive innovation, and build more resilient operations.

Data that does more good.
Achieve productivity and sustainability goals with our data-driven solutions.

Global leaders in Digital Transformation and Industrial Automation
Global leaders in Digital Transformation and Industrial Automation
We meet you where you are in your journey with market leading hardware, software, and services to make you more resilient, agile, and sustainable.
Latest Insights
Redefining What’s Possible and Achieving Results
Select your interest: