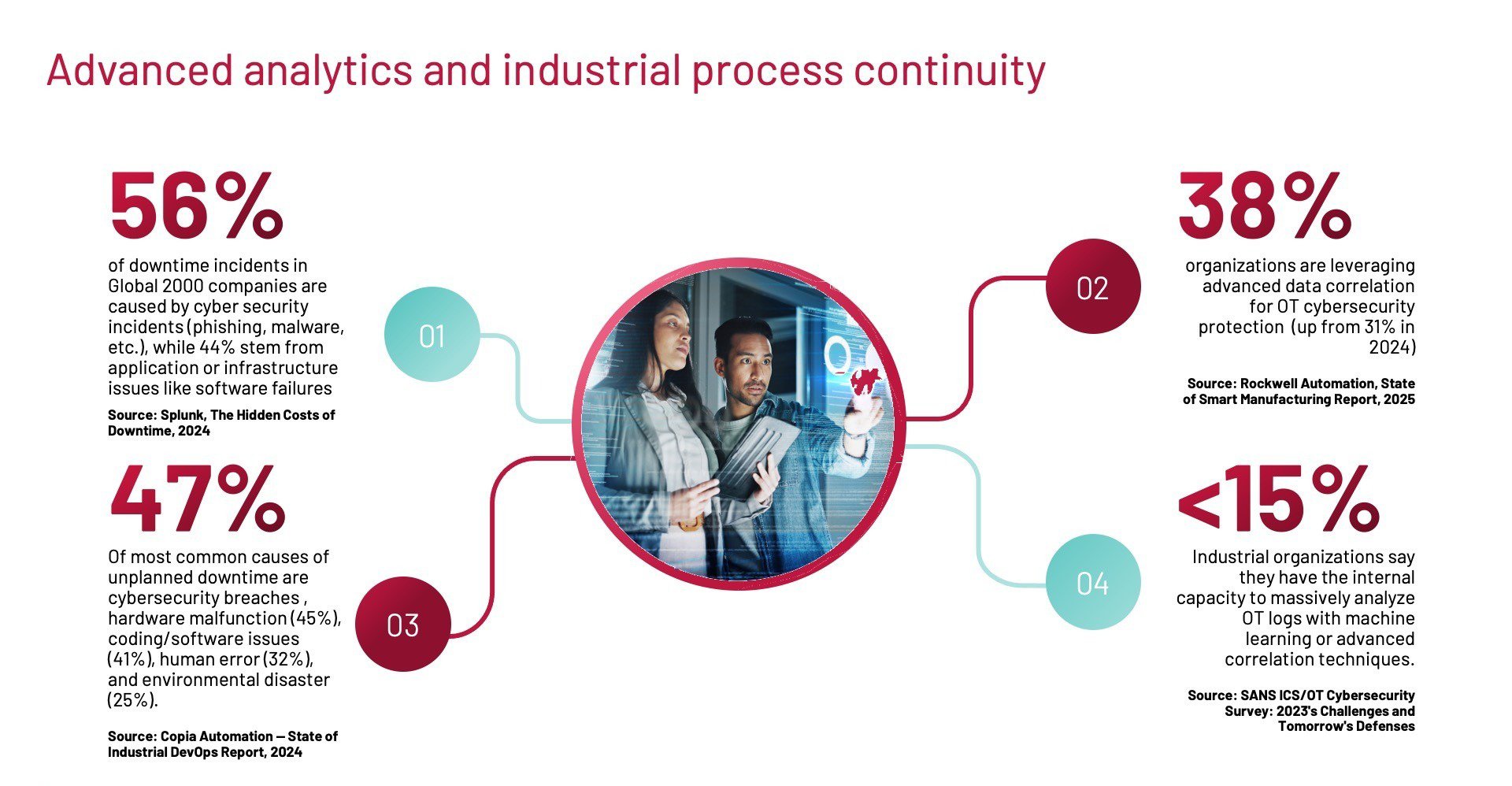
The availability of industrial manufacturing operations serves as a critical foundation for maintaining overall business sustainability. Any interruption in the process can impact production output and delay order fulfillment, therefore placing significant focus on the maintenance functions of the manufacturing operations. Over time, such disruptions may negatively impact revenue and increase the risk of contractual non-compliance with clients.
The Silos of Industrial Business Continuity
In many industrial organizations, formal responsibility for business continuity is typically across multiple departments, each with clearly defined roles and responsibilities that include:
General Management / Executive Committee
Exercising a leadership role and setting the continuity strategy and the approval of the necessary investments. These teams should also belong to the crisis management committee due to the need for decision-making (halting production, activating alternative plans, etc...).
Risk Department / Business Continuity Management (BCM)
In large organizations, there are specific teams in charge of risk analysis, creation of contingency plans and evaluation of regulatory compliance, which support and sustain management in making strategic decisions.
Legal and Compliance
Supervising the legal implications of the decisions made and the legal or regulatory needs of the company by their industry sector or geographical location in which they operate.
Finance (CFO/Treasury)
Finance teams collaborate in the evaluation and quantification of the financial impact of shutdowns and with the creation of contingency funds. They also deal with insurance, liquidity and, in general, economic risk management.
Information Technology (IT/CIO)
The role of the IT department, led by the Chief Information Officer (CIO), is becoming increasingly significant for business continuity. Given their strategic responsibility for managing the systems and networks that support core business applications, CIOs play a pivotal part in confirming the ongoing operation of corporate systems such as ERP, CRM, and IT networks. Additionally, they are essential to cybersecurity efforts, which typically center on information technology (IT) rather than operational technology (OT).
Human Resources (HR)
HR teams verify the availability of critical personnel. They are responsible for developing rotation schedules, establishing teleworking strategies, and defining emergency protocols related to personnel management.
Operations / Production
Although these teams are responsible for industrial process continuity (maintenance, SCADA, PLCs, MES) and are a critical part of business continuity, their vision is often not fully integrated into continuity plans at the corporate level.
OT Knowledge of Remaining Departments
Except for the production teams, the rest of the departments are usually unfamiliar with the functionality and criticality of OT assets. The areas of risk management, finance or compliance dominate risk management at the corporate level, but do not understand OT technology (PLC, SCADA, DCS, industrial networks) in detail. The IT department possesses strong technical expertise, particularly within its primary domains such as servers, databases, and corporate networks. However, professionals in this area typically have limited familiarity with OT protocols including EtherNet/IP, Modbus, Profibus, and OPC-UA. Human Resources primarily oversees personnel planning. Operational Technology expertise resides within the production department; however, production teams are frequently not directly engaged in formulating the corporate continuity strategy.
Why OT Risks Are Overlooked
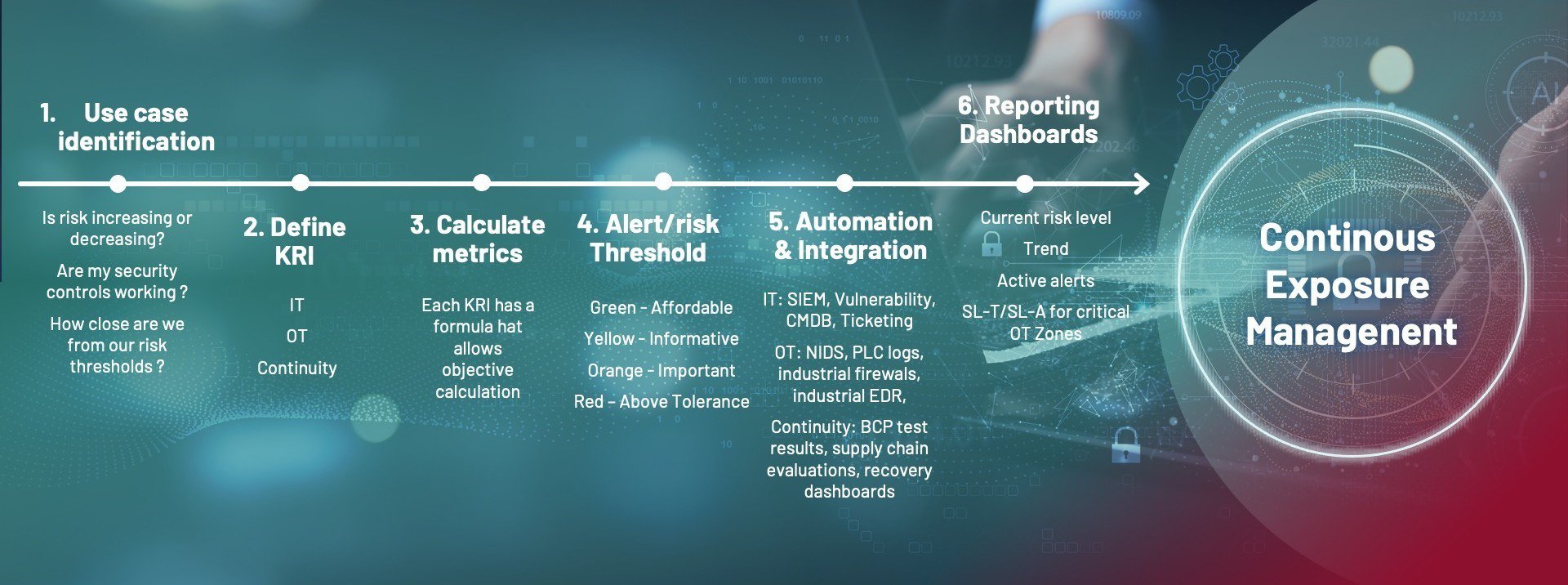
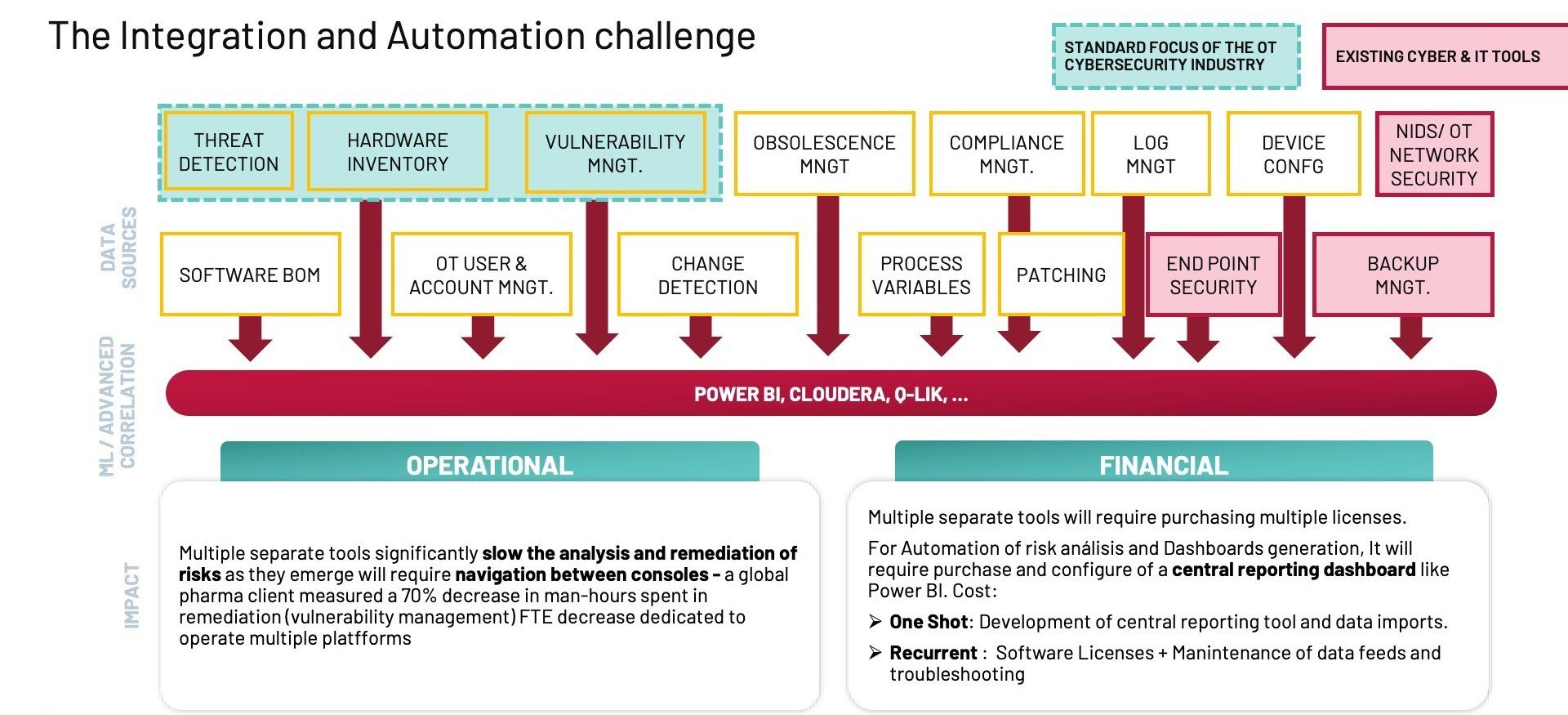
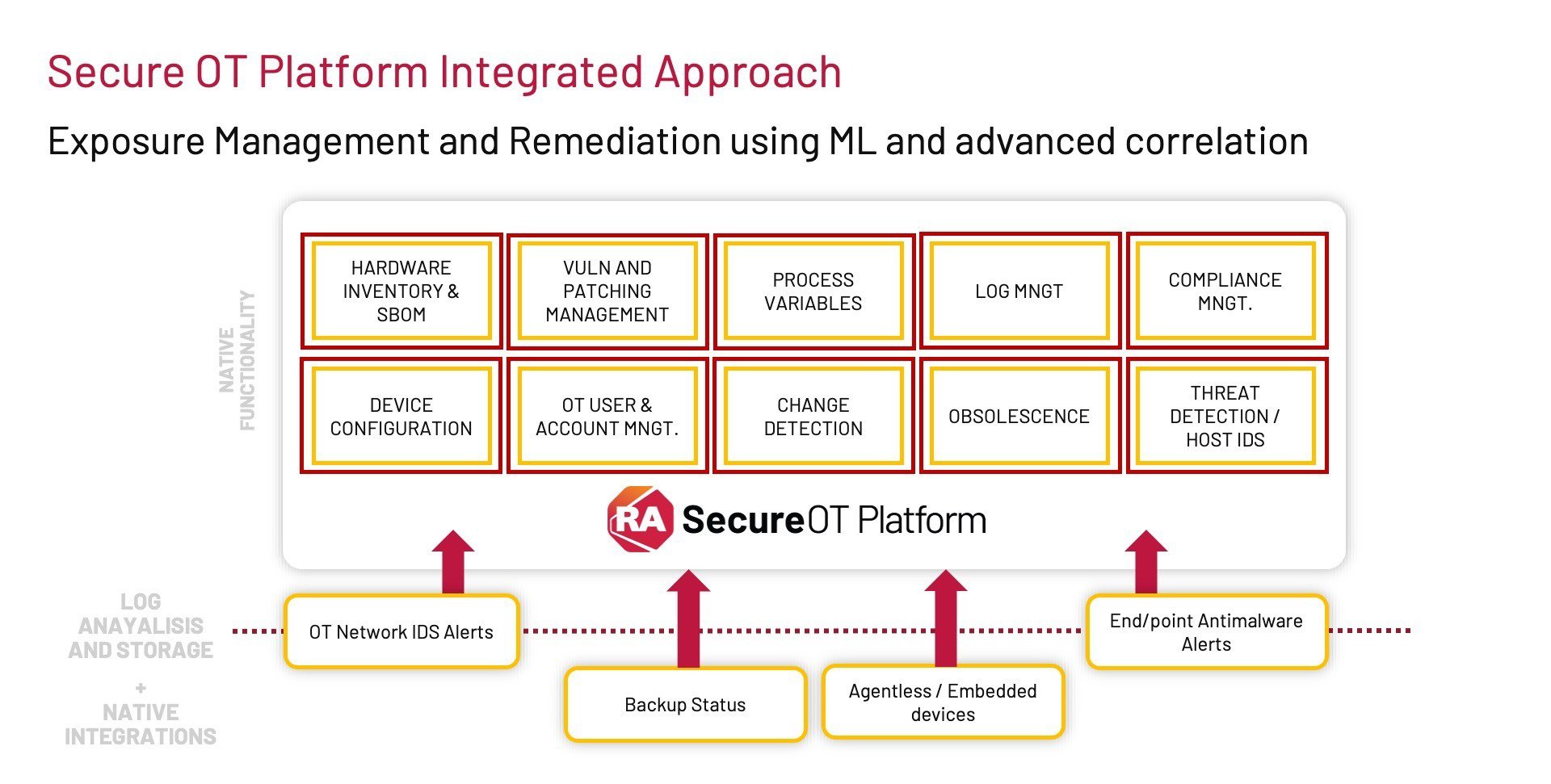
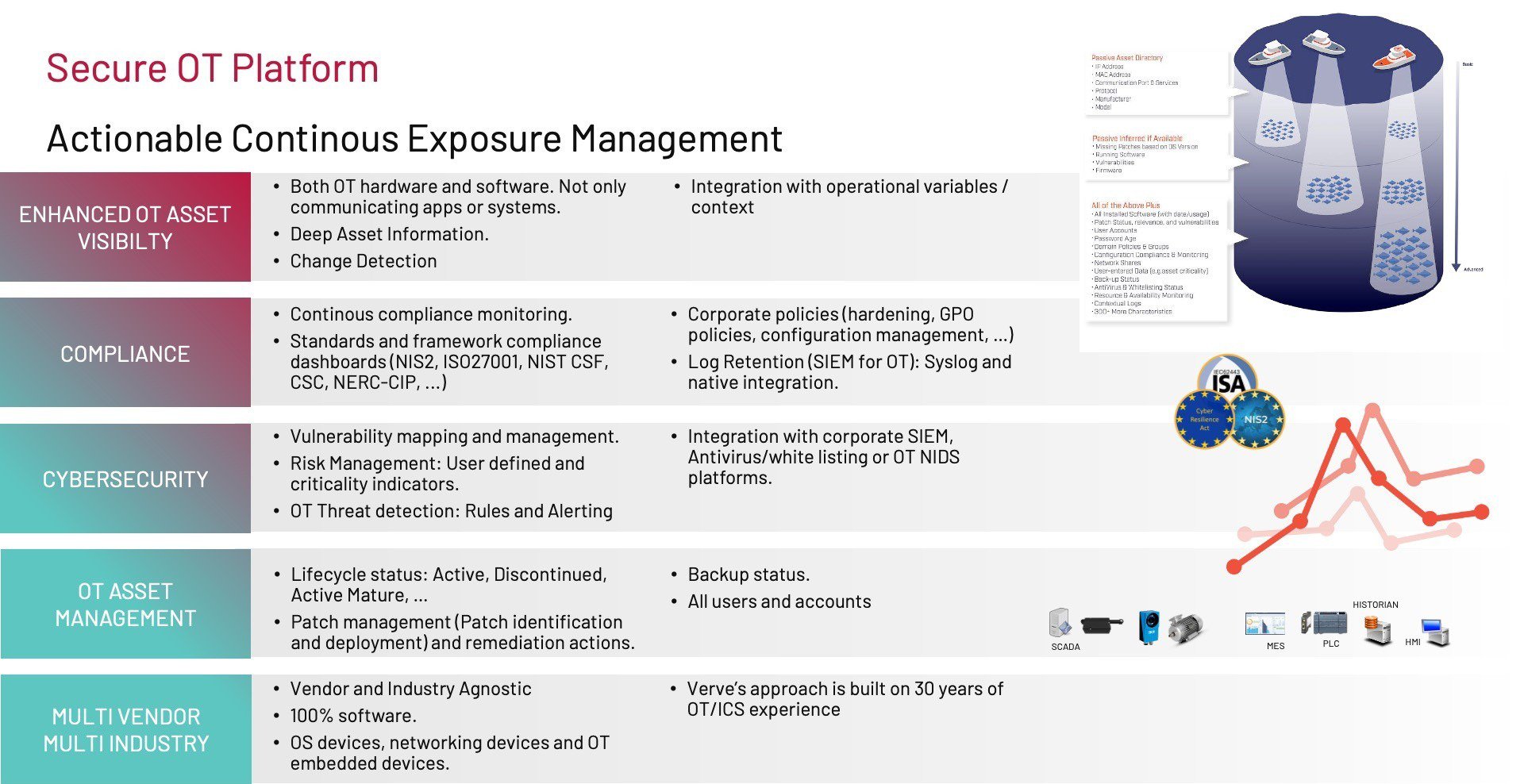
A distinct gap exists between corporate risk oversight and industrial process continuity at the operational or plant level (from the OT perspective). Bridging this gap requires continuous threat exposure management—a framework that ensures OT-specific vulnerabilities are visible to the entire organization. When these areas are not aligned, corporate functions may underestimate OT-related risks due to limited awareness. Consequently, production teams may not receive appropriate budget allocations to address OT vulnerabilities that could endanger overall business operations.
This recurring misalignment presents a significant challenge. Although risks impacting overall business continuity also influence process continuity, and vice versa, certain risks demand specialized expertise and understanding within the operational technology (OT) domain and related production systems. Neglecting operational risks can have substantial implications for achieving business continuity objectives. Given the varied nature of these risks, analysts must possess distinct levels of expertise to accurately identify and assess each risk category.